June 12th, 2024
Background checks are a crucial part of the hiring process, allowing employers to evaluate applicants’ suitability. Recent news about the cybercriminal organization USDoD selling personal information on the dark web has raised serious concerns about the security of background check data. This incident highlights the importance of strong cyber security measures to safeguard sensitive information during online background checks.
Lessons for Employers and Job Applicants:
Ensure third-party vendors have robust security protocols.
Use encrypted channels when transmitting sensitive data.
Implement access controls and regular system monitoring.
In line with these lessons, employers and job applicants must understand the significance of vetting background check providers.
Understanding Stolen Background Check Data and Its Impact
Stolen background check data refers to the unauthorized acquisition of personal and sensitive information collected during background checks. This data can include:
Social Security Numbers
Financial records
Employment history
Criminal records
Cybercriminals exploit this data in various ways, including identity theft. With access to such comprehensive personal details, criminals can open bank accounts, apply for loans, or commit fraud in the victim’s name.
Potential Consequences of Data Breaches
Data breaches in the context of background checks pose significant risks:
Individuals whose information is compromised may face substantial financial loss and damage to their credit scores.
Employers may suffer reputational harm if their handling of sensitive information is called into question.
Organizations could face legal actions and fines due to non-compliance with data protection regulations.
Understanding these implications underscores the critical importance of robust cyber security measures in protecting background check data.
The Growing Threat of Cyber Attacks on Background Check Services
Cybercriminal organizations consistently discover new ways to exploit weaknesses in background check service providers. These advanced groups use various methods:
Tricking employees with deceptive emails or messages to give away their login details.
Sneaking in harmful software to steal sensitive information from systems.
Targeting weaknesses in software security to gain unauthorized entry.
One notable example that highlights the seriousness of this issue is the USDoD data breach. In this incident, hackers successfully breached the Florida-based information broker National Public Data, which handles API searches for companies requesting background checks. They stole a large amount of personal data, which they later sold on the dark web. This incident serves as a reminder of the significant risks individuals and organizations face.
Building a Resilient Cyber Security Framework for Background Check Processes
Strong security measures are crucial for protecting sensitive data during background check processes. Organizations must establish comprehensive internal security protocols to safeguard against potential breaches.
Key Practices:
Implement strict access controls so that only authorized personnel can access sensitive information. These control measures include using multi-factor authentication and role-based access permissions.
Continuous monitoring of systems helps identify and respond to suspicious activities promptly. Utilize advanced threat detection tools and conduct regular audits to maintain system integrity.
Data integrity and confidentiality are paramount. Using encryption technologies and secure storage solutions can significantly enhance data protection.
Best Practices:
Encrypt data at rest and in transit to prevent unauthorized access. Adopt industry-standard encryption protocols to ensure the highest level of security.
Store sensitive information in safe, compliant environments. Use dedicated servers with advanced security configurations and regular backups to protect against data loss or corruption.
Following these best practices, organizations can build a robust cyber security framework, protecting sensitive information during background check processes. This proactive approach reduces risks and builds trust among employees and job applicants, highlighting the importance of data protection.
The integrity of background check data is a shared responsibility. Adopting robust cyber security measures ensures trust and safety in the hiring process.

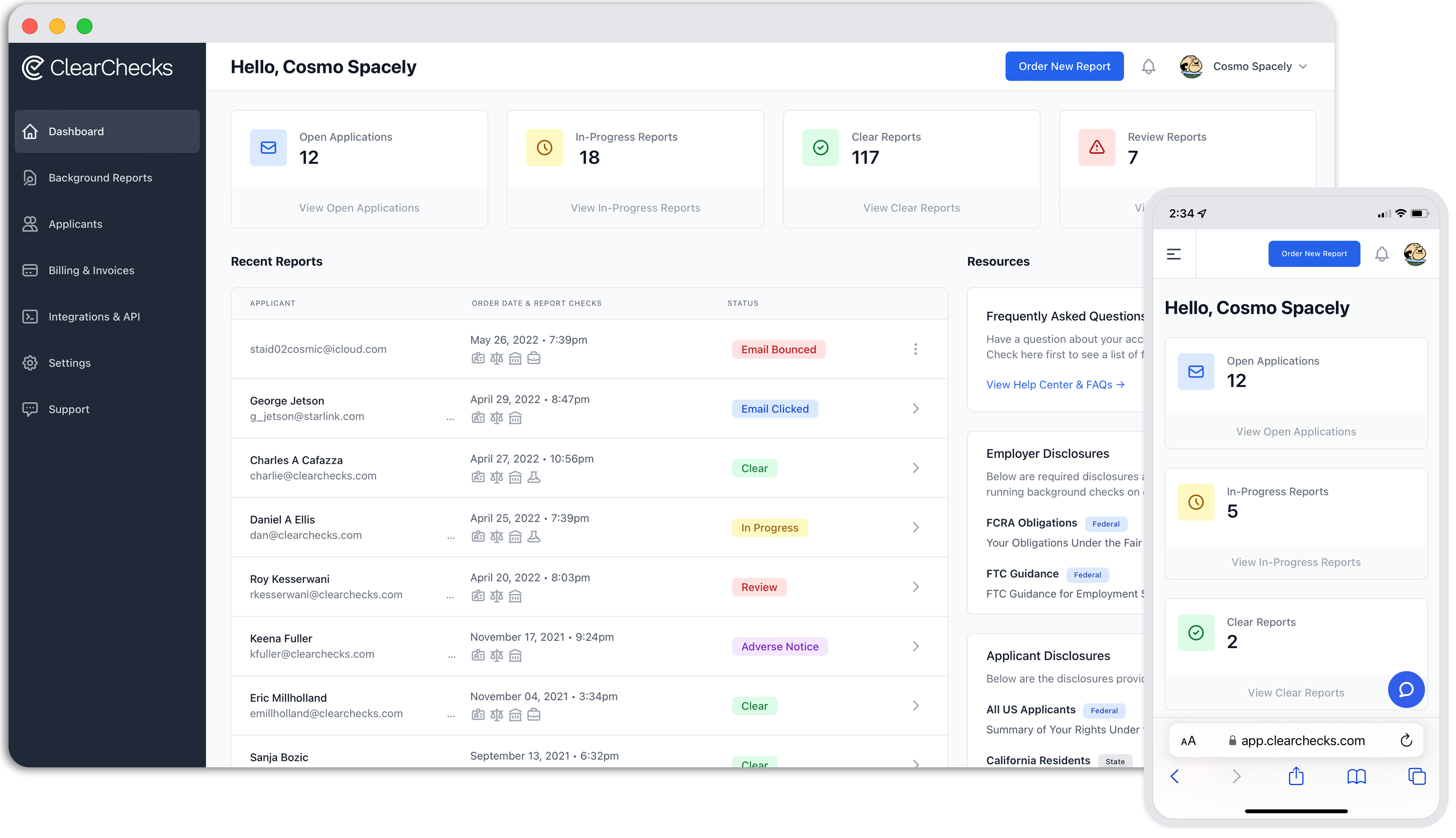
Need Background Checks?
See packages and pricing and order instantly.
National, County, Statewide, Federal Criminal Searches
Motor Vehicle Records
Employment & Education Verifications
Bankruptcies, Liens, & Judgments
Drug Testing
HireRight vs. BackgroundChecks.com: Which Background Screening Platform Fits Your Business?
Background Check Pricing in 2026: What You Should Expect to Pay (and How to Avoid Hidden Fees)
Drug Testing for Employers: 5-Panel vs. 10-Panel Options Explained
QSR Restaurant Staffing in 2026: A Practical Guide for Operators